Human Defense Methods to Measurably Improve Cybersecurity and Compliance
December 11, 2023 | By: Dr. James Norrie
Optimizing Human Defense Strategies: cyberconIQ’s Innovative Approach to Cybersecurity and Compliance
If you are on the cybersecurity or GRC team in your organization, you are often tasked with thinking about how to lower the risk of an external compromise through various controls and threat detection systems, training to improve user awareness, or imposing selective consequences on repeat offenders for instance. All of this is good and necessary work; but today it’s only organization table stakes.
 At cyberconIQ, we offer a deeper understanding of employees’ security habits and instincts borne of extensive proprietary research and using targeted and patented methods. We strive to develop more sustainable ways to address the more dangerous and less predictable risk of compromise when users deliberately chose a course of action that is outside of your policy boundary. We call this voluntary pathways to compliance. And we are experts at it.
At cyberconIQ, we offer a deeper understanding of employees’ security habits and instincts borne of extensive proprietary research and using targeted and patented methods. We strive to develop more sustainable ways to address the more dangerous and less predictable risk of compromise when users deliberately chose a course of action that is outside of your policy boundary. We call this voluntary pathways to compliance. And we are experts at it.
Why is this topic so relevant and timely? Regulators like the SEC, NIST and others have concluded that human vulnerabilities are the most likely source of a successful breach. When over 70% of successful attacks rely on a human factor to succeed (i.e. mistake, manipulation, or misintention), our profession must revisit existing methods and our past conduct attempting to reduce this risk because those efforts have obviously failed. And that failure is becoming more visible.
For example, recent surveys (Gartner 2023) report employees feel compelled to break their organization’s security policies and practices when they conflict with their job responsibilities, productivity goals, or which impose additional time constraints or technical burdens on already compressed workflows. Often, densely written technical security policies are distributed for employee acknowledgement and then promptly forgotten by all concerned. Worse, they often immediately begin to interfere with client, supplier or vendor satisfaction because the policies were conceived based on best practice or regulatory requirements; but not well-tested on internal workflows and systems. They are often impractical and, unless written in plain language, often hard for employees to understand and interpret in context. It is an untenable position to expect employees to comply with security policies that impose job friction when they are also managed to productivity goals concurrently. All that provokes is fear and then mistrust – and pits compliance against productivity. Fact: this proves the mere presence of policies will not consistently change employees’ day-to-day online compliance behaviors.
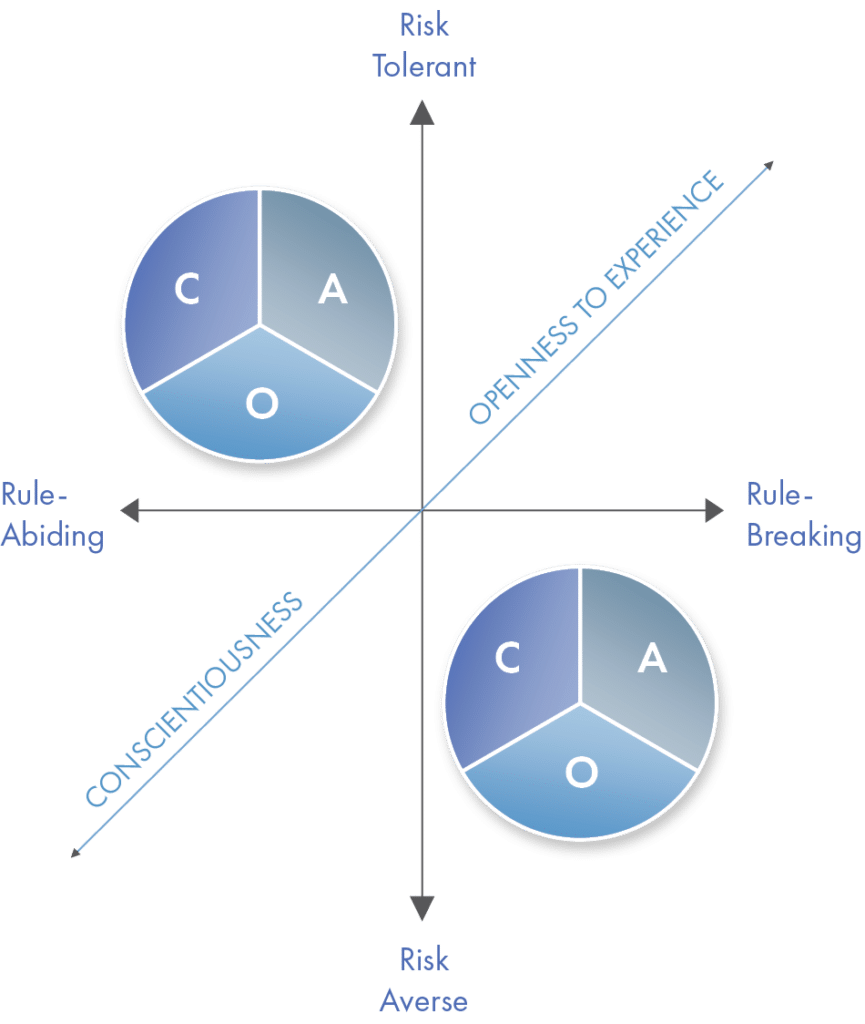
So, what will work? Our research proves an optimal approach to realizing better security and compliance behavior is to consider both base human instincts and improved security processes and workflows together. This blends technology and psychology to create opportunities for voluntary changes in internal security habits that creates a sustainable “Security 1st” culture to measurably reduce the real risk of security incidents and accidental data loss beginning instantly.
An essential ingredient of success is for security and compliance teams to acknowledge this dilemma and approach better solutions more collaboratively. Cybersecurity is not uniquely a technical problem – and so security policies and practices cannot be imposed without understanding human behavior – which then also demands knowledge of change management and organizational development best practices to succeed. Because we have so often approached cybersecurity as a technical discipline in the past, there may be an imagination that we can make humans “programmable” by simply insisting that they comply. Regrettably, this approach only causes employees’ to hide their non-compliant behavior or to mask it intentionally to look like compliant behavior when it is not.
At this critical time of rampaging seasonal threats that exploit the increased stress and elevated moods that holidays often provoke in many of us, maybe it’s time to reconsider your human factors cybersecurity program maturity? Are you really doing as much as you can and should to bolster your human defenses by improving your employees’ fundamental security judgement, instincts, and intentions to adjust them to being more effective in the face of increasing threats? That is all about behavioral science not computer science! If not, aren’t you knowingly leaving your most likely security vulnerability – humans – wide open to attack and exploitation in this age of AI-enabled security threats where you need to protect our organization more diligently than ever. To learn more, contact our experts at sales@cyberconIQ.com for your free assessment.

